Cellular Automata based Cryptography Model for Reliable Encryption Using State Transition in Wireless Network Optimizing Data Security | SpringerLink

Correspondence between cellular automata and cryptography according to... | Download Scientific Diagram

Theoretical Computer Science: Introduction to Automata, Computability, Complexity, Algorithmics, Randomization, Communication, and Cryptography (Texts in Theoretical Computer Science. An EATCS Series) | Walmart Canada

Buy Express Learning Cryptography And Network Security Book Online at Low Prices in India | Express Learning Cryptography And Network Security Reviews & Ratings - Amazon.in

Cryptography & Network Security: Buy Cryptography & Network Security by I. A. Dhotre, V.S.Bagad at Low Price in India | Flipkart.com
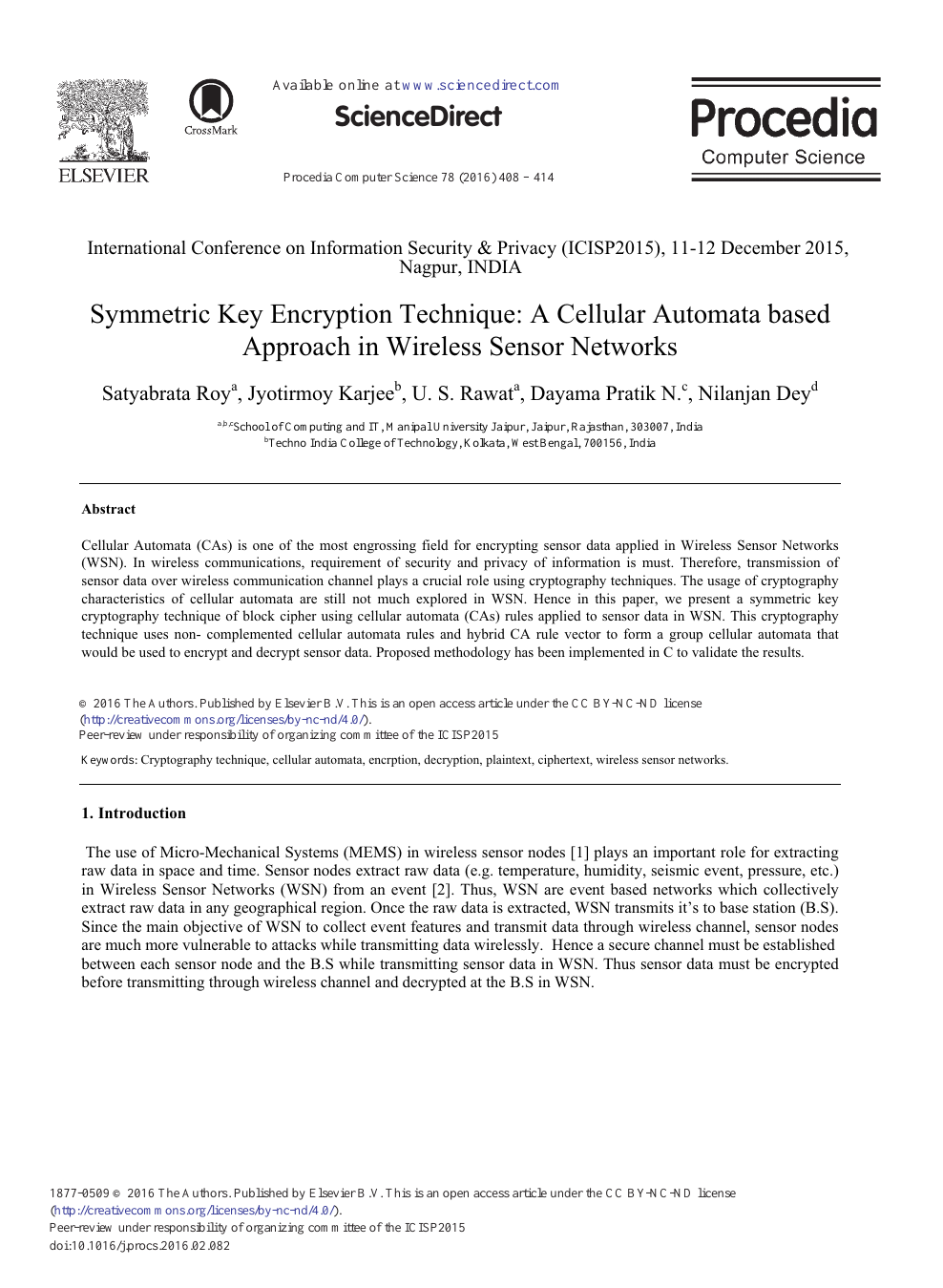
Symmetric Key Encryption Technique: A Cellular Automata based Approach in Wireless Sensor Networks – topic of research paper in Computer and information sciences. Download scholarly article PDF and read for free on
![PDF] A New Cryptographic Hash Function Based on Cellular Automata Rules 30 , 134 and Omega-Flip Network | Semantic Scholar PDF] A New Cryptographic Hash Function Based on Cellular Automata Rules 30 , 134 and Omega-Flip Network | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/1563c58daf7a9f63784ee19a98aeb529b7eb66bb/6-Table3-1.png)
PDF] A New Cryptographic Hash Function Based on Cellular Automata Rules 30 , 134 and Omega-Flip Network | Semantic Scholar
![PDF] A New Cryptographic Hash Function Based on Cellular Automata Rules 30 , 134 and Omega-Flip Network | Semantic Scholar PDF] A New Cryptographic Hash Function Based on Cellular Automata Rules 30 , 134 and Omega-Flip Network | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/1563c58daf7a9f63784ee19a98aeb529b7eb66bb/5-Table2-1.png)